SSL certificate is a good way to show the security of your blog. A hosted WordPress blog often requires a SSL certificate in order to use HTTPS. However, everyone understands that SSL certificate comes at a cost. Therefore, in order to reduce that cost to zero, let’s create a free self-signed ssl certificate. This would allow you to use https in the browser; however, some browsers might throw an error. Don’t worry, it can be resolved using a CA Certificate or Cloudflare SSL.
We are using Apache with Linux as a web server. Commands may be different on a server running using Windows. Definitely, SSL configuration for anything other than Apache is also different. However, if you are smart, then you can translate these instructions for any platform.
Self-Signed SSL Certificate on Linux with Apache
You need to login to server using SSH access. In case, you don’t have ssh login details. You can contact your hosting provider. On Windows, you can use Putty to operate your server using SSH.
Note: We’re assuming that you’ve enabled SSL for Apache, and etc/httpd/ssl exists in your installation. In case, you have not enabled SSL on your server, make sure you have enabled mod_ssl for Apache, and ssl.conf file exists in the folder mentioned above.
Navigate to, /etc/apache2/ssl or /etc/httpd/ssl, depending on your apache configuration path (CentOS has httpd folder, whereas Ubuntu has apache2 folder). Run the following command to create server.key and server.crt for your server. We’re assuming that you are using root for this, incase you are not on root. Append sudo in the beginning. The certificate is valid for 1095 days.
openssl req -x509 -nodes -days 1095 -newkey rsa:2048 -out /etc/apache2/ssl/server.crt -keyout /etc/apache2/ssl/server.keyAfter you press enter, you will need to answer a few questions. For example, Country name, state and Organisation name. These answers are used for the SSL certificate.
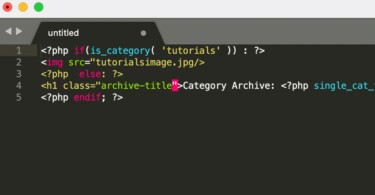
Now, you need to configure your SSL. Find ssl.conf, in CentOS it’s located inside /etc/httpd/conf.d/ssl.conf (the normal HTTP configuration includes this file to be called along with basic Apache configuration). In Ubuntu, the configuration is under the /etc/apache2/ssl folder. Edit the ssl.conf using nano (nano ssl.conf) and define your virtual host in this manner.
<VirtualHost *:443>
DocumentRoot /var/www/html/yourwebsite/public_html
ServerName www.yourwebsite.com
SSLEngine on
SSLCertificateFile /etc/ssl/server.crt
SSLCertificateKeyFile /etc/ssl/server.key
</VirtualHost>Further, you need to redirect HTTTP requests to HTTPS. Add the following line of code in your normal HTTP configuration, which is located in /etc/httpd/ or /etc/apache2/ under conf.d folder.
<VirtualHost *:80>
ServerName www.yourwebsite.com
Redirect "/" "https://www.yourwebsite.com/"
</VirtualHost>You need to restart Apache. Command for CentOS is systemctl restart httpd, this restarts httpd service. You can also check your Apache configuration before restarting your server using this command apachectl configtest.
Conclusion:
You noticed creating a self-signed ssl certificate is not an issue. You can also use DHParameters for ssl.conf which promise an increased security for encryption. The process of enabling a self-signed certificate is one and same on every Linux distribution. However, paths of SSL files and configurations are a little different. OpenSSL is an ultimate toolkit to generate certificates. You can get the certificate approved from a Certificate Authority, or use a Cloudflare self-signed certificate option to bypass browser error of SSL.